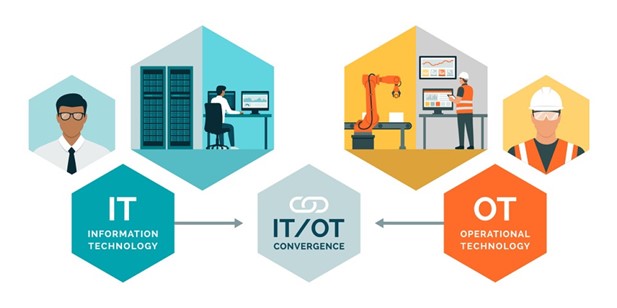
AI, IIoT, OEE, OPC-UA, MQTT ... Anyone looking to delve into Industry 4. 0 will be hit with the necessary abbreviations. The two most important ones? They may not even be in that list yet. Because what we really want to achieve with Industrie 4.0, one connected factory, is all about connecting information technology (IT) with control technology (OT). Only then can data start flowing freely between processes to realize those intended gains in efficiency, quality, productivity .... With one major concern: cybersecurity. After all, the NIS 2 legislation requires manufacturing companies to adequately arm themselves. And that requires experts with knowledge of both worlds.
In an IT environment, everything has been about cyber security for years. The use of firewalls, antivirus software, encryption ... tightly secures everything so that intruders have less chance. So if it takes a second longer before you get that mail in your inbox, no one will bat an eyelid. Copy paste to the production environment? Unfortunately not. Production continuity is paramount in this environment. There, communication just has to be in real-time, but that just brings more cyber risks. How on earth do you go about reconciling those two worlds? "From the hardware," opens Marnix Snijers, IT network specialist at APS, subsidiary of ATS Group. "For years we have been building the networks to enable all those automation processes, deep in production. Together with the customer, we look at what communication he wants and what it takes to set it up securely, from simple to complex networks, from the office to production. Always while maintaining the necessary separations between networks."
Knowledge of automation layer required
ATS' BU Automation adds its knowledge of automation processes. "Because, above all, it has to remain workable for everyone on the production floor. If OT is down, though, production and making money is done. And for that, you need sufficient knowledge of the automation layer. A new machine or installation? In the past, it was simply plugged into the network at so it could communicate with other machines. Efficient, yes, cyber-secure, no," explains OT network specialist Sammy Van den Meersschaut. "That there is a need in production for more cyber security, production companies are gradually becoming aware of that. The stories that hit the media about how hackers managed to completely paralyze certain companies show that things have to be different. That there must be separation, physical or virtual. The Cyberfundamentals Framework with the NIS 2 guidelines are available today from the Centre for Cyber Crime Belgium https://ccb.belgium.be. This is a wake-up call, it becomes law by Oct. 17, 2024. It is of need now."
NIS 2 in a nutshell
Van den Meersschaut summarizes the main thrust of this directive. "First, you have to map out the traffic and participants in your network. Then you analyze exactly what that traffic means and what actions should be linked to it. Finally, you also need a plan so that if things do go wrong, you can return to a safe situation?" An approach that is familiar in principle, but to which (financial) responsibility is now attached. "The manager of a company must be able to prove that he has done everything possible to contain the risks of a cyber attack. A figure is even put on that: Fines can be 1.4% of total revenue." Although a company's scale determines whether it must comply or not, Van den Meersschaut predicts that everyone will be pulled into the bathtub with it. "They will impose the same compliance on suppliers and partners."
Collaborate
Better back to Industry 3.0 then? "There are still many customers who operate stand-alone, separate from the network. But besides the added value that the smart use of data can bring to your production, it is also becoming a trend among machine suppliers to demand more openness. They prefer not to put their engineers on a plane for repairs so quickly anymore and demand to make access via remote access. A situation that sets off all the alarm bells in cyber security terms," says Automation BU manager Bert Deslee. "We see that the line between IT and OT is getting thinner and thinner. They don't walk through each other just yet. But that means that those responsible for production and from the IT department will have to work together to achieve cyber-secure production. Each environment has its own requirements and hardware solutions. Together, as ATS and APS, we help our customers establish a secure architecture for a high-performance and future-proof OT-IT environment."

Segmentation for secure connectivity
In such a cyber-secure environment, the key word is segmentation. "We have to get rid of so-called flat networks. Separating the IT and OT networks is a good start. But that does not mean that no communication should be possible between the two. On the contrary, but it must be done in a controlled, secure way," said Snijers. And then just that knowledge of and IT layer via APS and the OT layer via ATS comes in handy. "For example, we know how SCADA, MES and ERP systems are technically connected, what protocols are present in a PLC. In other words, we know what is needed for secure connectivity," Deslee adds. The same story must then be extended into production itself. "The more systems that can be separated from each other, the less impact an outside penetration can have. Switches and firewalls can then control traffic between segments. This is how you build a security architecture step by step, layer by layer," Van den Meersschaut says.
Technical best solution
The right hardware lays the foundation, software then provides cyber-secure control of traffic. One such product that APS and ATS work with is Claroty. Says Snijers, "It maps the network, visualizes it, so it also makes it easier to detect anomalies and unauthorized access. To set up a centralized remote access solution. Or to check off updates, patches and firmware." So the technology is there today to reconcile IT and OT, but everything starts with raising awareness. "Only when customers realize what one cyber-attack can cost them will they be willing to dedicate the necessary resources to it. In the OT world, systems might last for 20 years. In IT, software is dated after five years. Cybersecurity is also about keeping up, and that requires a good partner. Techies who don't try to sell software or hardware, but who help look for the technically best solution. And this is unique for each customer," Deslee concludes with a wink.
